Creating phishing website is the most prominent way to steal sensitive user data. Hacker’s implement this method time and again successfully. Earlier we have discussed installing and configuring Kali Linux. The Linux distro comes with a toolkit designed for hackers. Kali Linux best works with the Virtual Box rather than installing it in dual OS mode.
Social Engineering Toolkit (SET):
This is an integral part of Kali Linux. To access the toolkit you need to have root access to the system. Social Engineering Toolkit (SET) helps in designing your phishing attacks. Today we will discuss the most prominent way the phishing website attack for hacking username password.
In this attack a website clone is created which looks exactly same as the original website. The website is hosted on an external server. So any http request sent to the server will display the cloned page. Now why will any one visit your server. That is the trick which you need to understand.
Steps to create a phishing website for hacking username password:
1) Open the terminal window in your Kali Linux.
2) As pointed out earlier to access the SET you need to have root access. If you are not at the root prompt type,
sudo root
3) At root prompt type,
setoolkit
4) Enter 1 to Select ‘Social – Engineering Attacks’.
5) Enter 2 to ‘Select Website Attack Vectors’.
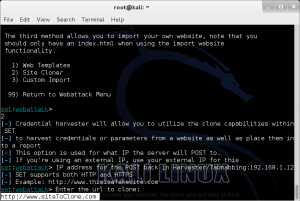
6) Since we intend hacking username password i.e credentials through our phishing website we need to enter 3 ‘Credential Harvester Attack Method’.
7) Since we need to clone the site we need to enter 2 for ‘Site Cloner’.
8) It will ask for IP address for the post back in Harvester/Tabnabbing. Enter the IP address of an external server, where you will be hosting the website. For example if you enter the ip address as 192.168.1.12, when anybody visits the url http://192.168.1.12 the user will be shown the webpage of the cloned website.
9) Enter the url to clone, here we need to enter the site you want to clone so enter it http://www.siteTo BeCloned.com.
You have now cloned the website and hosted it on the server. Remember the page that you are cloning should be the log in page of the website where user enters the credentials. Now as we have discussed no one will visit the ip address so here the url shortener services like bitly.com, goo.gl, yourls.org, tiny.cc to name a few. Create a shortened url and share it on forums so that users click and follow the url to your phishing website.
Whenever the user enters the credentials and submits it, the data is sent to your SET and you will see the users credential displayed on your screen. This is how the SET helps in hacking username password by creating phishing websites.
Safety tip for users against SET attack:
It is always advised by financial institutions to its users that they should not follow a link to visit the internet banking portals. Always check the url in the browser before entering your credentials.
The cloned website url’s are either ip addresses or a small difference in the name. Example if a legitimate website address is http://www.yourBank.com the cloned website could be http://www.yourBank.co.uk, a difference that could go unnoticed.
Disclaimer: The article is for Educational purpose only. The website and the author are not responsible for any unlawful use of this article. Please don’t misuse the information.







I’m curious to find out what blog platform you are utilizing? I’m having some small security problems with my latest website and I would like to find something more secure. Do you have any recommendations?
I think this is one of the so much important information for me. And i’m satisfied reading your article. However want to remark on few common things, The web site style is perfect, the articles is in point of fact excellent : D. Good process, cheers
Just wish to say your article is as astounding. The clearness on your put up is simply nice and i can assume you are an expert on this subject. Well together with your permission allow me to take hold of your RSS feed to keep updated with drawing close post. Thanks 1,000,000 and please keep up the rewarding work.
I’m not sure exactly why but this website is loading incredibly slow for me. Is anyone else having this issue or is it a problem on my end? I’ll check back later on and see if the problem still exists.
Is it is possible to attack a victim without knowing victim ip. Is there is some other method to attack the victim.
IP address isn’t confidential. It changes always after 1-2 hours dynamically. Yes, it’s completely possible. You can use Bruteforce
i tried alot and works properly with the victims on the same network but what about those r in different networks..
This article will assist the internet viewers for creating new web
site or even a weblog from start to end.
You are a genius
This clone page not opening in Android
Any solutions???
well done,nice article,awaiting for upcoming article
Hello, i have a problem with setoolskit, all works but when i write te name and password the TXT file is in blank! I am virtualizar the kali linux in a windows 10 host. Do you know how to solve this problem?
This Works Only if Users are on Same Network or [LAN].Is there is any way to make a phishing webpage to share it with my friends who are not on same network.
Oh there is its very powerful tool over WAN with a combination of DNS spoofing url redirecting, port-forwarding, and if you can integrate hyper-link naming after that too? you could fool anyone.
There is. But I probably didn’t state that its obviously not legal to do without consent and mostly used for educational, fun, and awareness purposes. Sorry there mods! 😀 this is something better spoken in private messaging, I didn’t mean to promote careless use of credential harvester.
Lets be fair though, this tool IS used over LAN and we all know it falls into the wrong hands and anyone determined will use it for the wrong reasons. But the idea that harvester is used over WAN is a fact, just ignoring it wont change this.
It is not as simple to construct but it is certainly worth noting how powerful a tool this can be. And half-decent hacker can figure it out pretty easily.
I’ll try but its simple complication with that, my credentials harvesters not send victims id.
My kali linux is virtual box based os, any solutions pls suggest me my friends