A recent research in cryptography has brought out a way to crack the cryptographic algorithms with just bare hands. Daniel Genkin, Itamar Pipman and Eran Tromer of the Tel Aviv University have submitted paper and given presentation on this topic at the CRYPTO 2014 conference held in California.
What does cryptography mean to us as users?
Cryptography taken from Greek word kryptos meaning secret and graphein meaning writing so it just translates to a ‘secret writing’. Formerly during war days the message sent across to soldiers were encrypted, which means they would just mean nothing to a third person if the message was intercepted by him. Only the person intended to receive the message could decrypt and understand the message.

In the modern world where even the ‘secured systems’ are not safe. The sensitive data that is sent from the system is encrypted so that the intended recipient is only able to read the information.
To make it simple we will discuss a scenario where you log in to your banking system. What you do is you send your user and password to your banking server. The server confirms the credentials and then authenticates you to access your account information. Suppose if a hacker intercepts this communication in transit. This will give him access to your credentials that you had sent to the banking server.
Thus the data is encrypted in a manner it becomes unusable for the hacker who intercepts it in the transit.
Crack and Hack encrypted info with bare hands:
This is possible by initializing attacks using novel side channels and are based on the observation that the ‘ground’ electric potential in many computers fluctuates in a computation dependent way.
Which means the processors computation signals can be felt by hand by just having contact with the exposed metal part of the laptop.
Processing signals behave differently for different computations thus making it easy to differentiate between encrypted signals. These electrical potential in computers fluctuates according to the computation that is being performed by its processor. The electric potential can then be measured through software for further analysis.
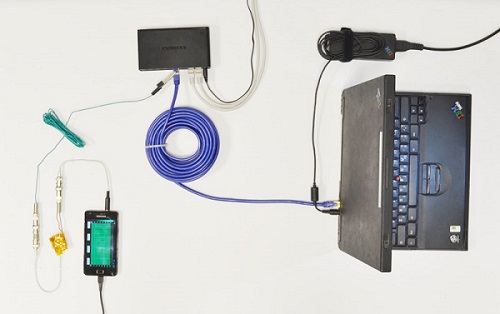
Though Complex equipment makes it easy to crack and hack encrypted info, the attack was successfully carried using Samsung S2 as per the paper. Through Cryptanalysis and Signal processing the computer experts were successful in extracting 4096-bit RSA keys and 3072-bit ElGamal keys from laptops.
